SentinelOne Singularity Platform: Comprehensive Guide from Architecture to AI-Powered XDR

Introduction: The New Paradigm of Autonomous Security
Modern cybersecurity threats have reached a level that exceeds traditional defense mechanisms in terms of speed and complexity. In this new threat landscape, the SentinelOne Singularity Platform offers an autonomous paradigm that fundamentally transforms reactive and siloed security approaches. The platform provides integrated protection by combining endpoint protection (EPP), endpoint detection and response (EDR), extended detection and response (XDR), and identity-based threat detection and response (ITDR) into a single unified platform.
SentinelOne's architecture is built on three core principles:
- Single Agent: A unified, lightweight agent for all endpoints.
- Autonomous Decision Mechanism: Local AI that detects and blocks threats with zero latency, even without cloud connectivity.
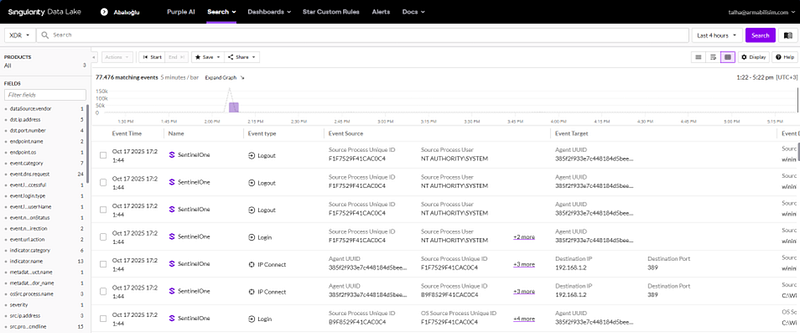
- Unified Data Plane (Singularity Data Lake): A centralized data layer that provides cross-domain analysis and holistic threat hunting.
This guide comprehensively examines the platform's architecture, threat detection methods, AI integration, and XDR capabilities.
1. Platform Architecture & Security Components
SentinelOne offers a multi-layered security architecture. The "single agent — multi-engine" design monitors file system, process, and memory activities in real-time at the operating system kernel level.
Resource Efficiency
The lightweight agent is optimized for performance:
- CPU Usage: 0–4%
- Memory Usage: ~20MB
- Disk Space: ~200MB
Autonomous Endpoint Intelligence
The most critical feature is the ability to run detection and response logic locally. This "on-agent" intelligence ensures protection even for isolated networks or critical infrastructures.

2. Multi-Layered Threat Detection Engines
SentinelOne analyzes files and processes in two main phases to provide protection against zero-day threats and unsigned attacks:
- Static AI Engine (Pre-Execution): Evaluates file structure and code properties before execution. It blocks malware without requiring signatures or hashes.
- Behavioral AI Engine (On-Execution): Monitors interactions like API calls, network connections, and system changes in real-time. It is designed to detect fileless attacks and "Living off the Land" (LotL) techniques.

3. Contextual Analysis: Storyline™ Technology
Patented Storyline™ technology automatically correlates thousands of raw EDR events into a single understandable attack story. Every event is tagged with a "Storyline ID," allowing analysts to see the entire attack chain—from origin to impact—in a single visual interface. This reduces root cause analysis (RCA) from hours to seconds.
4. Incident Response & Security Automation
SentinelOne provides advanced tools to neutralize threats quickly and restore systems to a clean state.
- Isolate Device: Automatically disconnects a compromised device from the network while maintaining a connection to the management console to prevent lateral movement.
- 1-Click Remediation & Rollback: Uses Windows VSS (Volume Shadow Copy) to undo damage caused by ransomware. It restores system settings and files associated with a malicious Storyline to their state just before the attack.
- STAR Rules (Storyline Active Response): Allows teams to create custom detection and response rules. Analysts can convert S1QL queries into persistent, autonomous detectors.
Deep Visibility & S1QL
Telemetry data is stored for 14–90 days and can be queried using the simplified S1QL language. For example, to list processes running specific commands in the last 180 days:
SELECT Timestamp, DeviceName, ProcessName, CommandLine
FROM ProcessActivities
WHERE LOWER(CommandLine) LIKE '%net user%' AND Timestamp > NOW()-180d;
5. The Autonomous SOC: Purple AI & Hyperautomation
With its "Autonomous SOC" vision, SentinelOne leverages Generative and Agentic AI to move security operations to machine speed.
- Purple AI: An AI security analyst built into the platform. It supports natural language querying (e.g., "Show me PowerShell activity last 24h") and automated triage, reducing MTTR (Mean Time to Respond) by up to 55%.
- Singularity Hyperautomation: A no-code automation engine for creating complex security playbooks using a drag-and-drop interface.
- AI-SIEM: Algorithmic analysis running on the Singularity Data Lake, detecting anomalous patterns that traditional rule-based SIEMs might miss.
6. Extended Detection and Response (XDR) Capabilities
SentinelOne extends protection across the entire enterprise attack surface:
- Singularity Cloud Security (CNAPP): Combines CWPP (runtime protection using eBPF technology for Linux) and CSPM (identifying misconfigurations). The acquisition of PingSafe added powerful agentless capabilities.
- Singularity Identity Security (ITDR): Protects Active Directory and Azure AD. It includes Deception Technology, creating fake credentials to mislead and trap attackers.
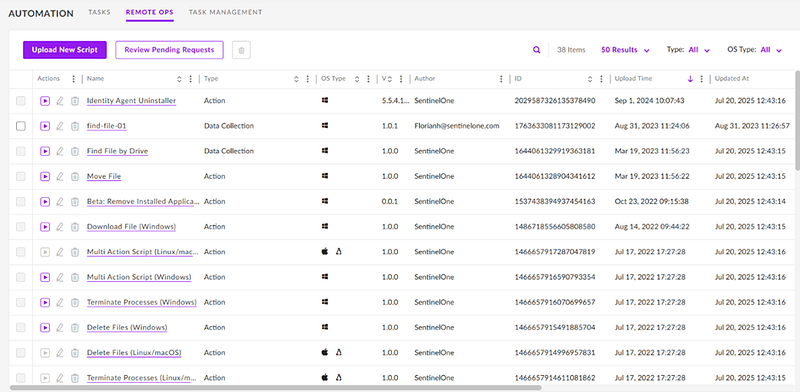
- RemoteOps Forensics: Centrally orchestrates digital forensics (DFIR) across thousands of endpoints, allowing for remote evidence collection and immediate response.

7. Policy Management & Security Configuration
The platform offers granular control through hierarchical policies:
- Modes: Detect-Only (Alerts only) vs. Protect (Automatic blocking).
- Control Modules: Device Control (USB blocking), Firewall Control, and Network Control (Ranger) which discovers unmanaged devices on the network.
8. Licensing & Ecosystem
SentinelOne offers a flexible model based on corporate needs:
- Core: Basic NGAV.
- Control: Adds device and firewall management.
- Complete: High-end EDR, behavioral AI, and RemoteOps.
- Commercial: Includes ITDR and WatchTower threat hunting.
- Enterprise: Full scale with Purple AI and custom modules.

Conclusion: Strategic Value
SentinelOne Singularity Platform is not just a security tool; it's a strategic business partner. By breaking down silos and responding at machine speed, it consistently earns 100% detection success in MITRE ATT&CK tests while producing 88% fewer alerts than the industry average. For organizations looking toward the future, it offers a sustainable path to secure-by-design infrastructures and the security of artificial intelligence itself.