SentinelOne Singularity Platform: Advanced Cybersecurity Solutions and Architecture Analysis Link to heading
Executive Summary Link to heading
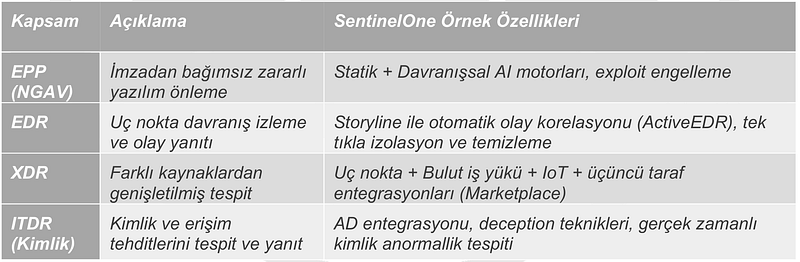
SentinelOne Singularity Platform offers an artificial intelligence (AI) supported and autonomous solution against today’s rapidly changing cyber security threat environments. The platform provides integrated protection by combining various security features such as endpoint protection (EPP), endpoint detection and response (EDR), extended detection and response (XDR), and identity-based threat detection and response (ITDR) into a single platform. In addition to being positioned as a “Leader” for the fourth consecutive time in Gartner’s 2024 Magic Quadrant report, MITRE attracts attention with 100% detection success in ATT&CK tests.

SentinelOne’s features include critical functions such as the ability to work offline, automatic incident response, and file rollback. This platform makes security operations more efficient by offering organizations fast installation, high detection success and integrated visibility. Additionally, it strengthens the cyber security infrastructure of institutions by supporting Zero Trust strategies.

This report comprehensively examines the SentinelOne Singularity Platform’s architecture, threat detection methods, management console components, identity security module, licensing options and comparative analysis with competing products. Additionally, sample scenarios are supported with MITRE mappings and application recommendations.
SentinelOne Singularity Platform Architecture and Security Components Link to heading
SentinelOne Singularity Platform offers a multi-layered security architecture, combining not only endpoint protection but also threat detection and response. The “single agent — multi-engine” architecture increases business efficiency by delivering all these security functions through a single agent. The lightweight SentinelOne agent runs at the operating system kernel level and monitors file system, process and memory activities in real time.
On this platform, two basic artificial intelligence engines, such as Static Artificial Intelligence (AI) engine and Behavioral Artificial Intelligence engine, work in an integrated manner. The static engine blocks threats in advance by evaluating the file’s structure and code properties without considering its signature or hash. The behavioral AI engine detects abnormal behavior by monitoring interactions such as inter-process relationships, API calls and network connections. These structures provide critical protection, especially against zero-day threats and unsigned attacks.
Autonomous Decision Capability: SentinelOne can make autonomous decisions to analyze and respond to threats. Agents can detect and block threats even without an internet connection. This is especially important for isolated networks or critical infrastructures.
Centralized Management Console and Scalability: SentinelOne’s centralized management console can be configured as cloud-based or on-premise. Thanks to its multi-tenant architecture, role-based access controls can be defined for different teams. Additionally, it has an elastic infrastructure that can manage more than 500,000 agents.
Threat Detection and In-Depth Visibility Link to heading
SentinelOne Singularity Platform provides comprehensive protection against known and advanced threats with a multi-layered threat detection architecture. This architecture analyzes files and processes in both phases:
- On-Write Static Analysis: Before the file is written to the disk, its structure and code features are evaluated and threats are prevented in advance.
- On-Execute Behavioral Analysis: When the file is executed, abnormal behavior is detected by monitoring transactions within the application, API calls, network connections and changes in the system.

This approach offers a critical advantage, especially for zero-day threats (0-day) and unsigned attacks. SentinelOne also allows security teams to perform deeper analysis by visualizing the contextual timeline of events with its Deep Visibility module.
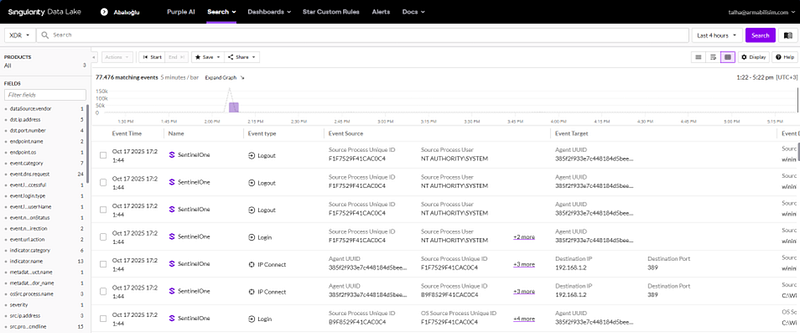
Deep Visibility module transforms SentinelOne from a classic prevention tool into a full-fledged security operations platform that enables contextual understanding of events and rapid response.
MITRE ATT&CK Mappings and Storyline Technology: SentinelOne is directly related to the MITRE ATT&CK framework and threats are visualized in the context of the timeline. Storyline technology allows analysts to review events more quickly and accurately by tagging each event with a “Storyline ID.”
Incident Response and Security Automation Link to heading
SentinelOne provides advanced incident response and security automation for fast and accurate response to cyber threats. These features ensure that threats are quickly neutralized and installations are easily rolled back.
Isolate Device: When critical threats are detected, the device is isolated from the network, providing access only to the management console. This prevents lateral movement and data exfiltration attempts.
Agents; It constantly records events such as processes, file operations, network connections, sessions and memory activities. This data is stored for 14–90 days depending on the license package and can be analyzed with SentinelOne’s simplified query language S1QL. Thanks to this language, which does not require technical knowledge, processes that have run the “net user” command in the last 180 days can be easily listed, for example:
SELECT Timestamp, DeviceName, ProcessName, CommandLine
FROM ProcessActivities
WHERE LOWER(CommandLine) LIKE '%net user%' AND Timestamp > NOW()-180d;
1-Click Remediation & Rollback: After threats such as ransomware, files and system settings can be quickly restored. The platform stores file versions prior to the attack, ensuring secure retrieval of data immediately after the threat.

The Automation / RemoteOps tab on the console allows running batch or scheduled commands on endpoints at the time of an incident or during routine operations. For example, operations such as service shutdown, log collection, or memory dumping for forensic analysis can be applied to hundreds of devices simultaneously.
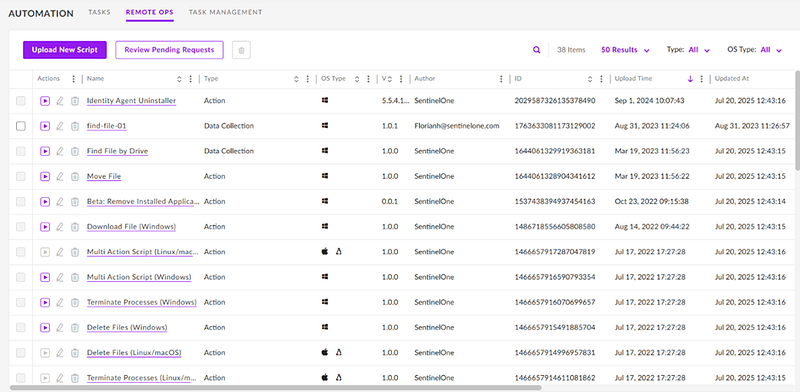
Additionally, thanks to API-based integrations, SentinelOne can trigger automatic actions with other security and IT systems. For example, when a SIEM rule detects a suspicious account lockout, SentinelOne can find and automatically isolate the devices to which that account is connected via the API.
Policy Management and Security Configuration Link to heading
SentinelOne offers policies that can be customized according to the different needs of organizations. These policies provide granular controls over devices and network segments, allowing different security levels to be defined. Policies can operate in two main modes:
- Detect-Only: In this mode, threats are detected but not intervened. Only warning is generated.
- Protect: Threats are detected and blocked automatically.
The main types of policies that can be defined in the SentinelOne console are:
- Threat Protection: Static and behavioral AI thresholds, automatic response behaviors.
- Device & Firewall Control: Blocking USB devices, port-based access restrictions.
- Network Control (Ranger): Agents detect devices that do not have agents installed by reconnaissance in network segments.
- Exclusions: File, directory or hash based exception definitions. This area should be used with caution; Excessive exception definitions can create security blind spots.
Policies can be governed by hierarchical inheritance; Rules defined at the top level can be customized in subgroups. It can also be exported and version controlled in JSON format, making it easy to track and roll back changes.
Licensing, Packages and Deployment Options Link to heading
SentinelOne offers a flexible licensing model based on corporate needs. Different packages can be configured according to the scale and security requirements of organizations:
- Core: Basic NGAV and limited EDR features.
- Control: Includes management capabilities such as device and network control (USB, firewall).
- Complete: The most popular package, offering advanced features like behavioral AI, XDR integrations, 14-day telemetry retention, and RemoteOps.
- Commercial: Identity security features such as the ITDR module and WatchTower managed threat hunting.
- Enterprise: Unlimited scale includes custom AI modules (Purple AI, Agentic SOC Analyst).

Integrations and Ecosystem Link to heading
SentinelOne provides a broad integration ecosystem by offering more than 70 ready-made integration modules. These integrations work with various systems such as SIEM, SOAR, ITSM, IAM, NGFW, MDM/UEM, cloud services (AWS, Azure), and DevOps tools.

Thanks to these integrations, the platform enables the transfer of event data, triggering of automatic actions and central management of security operations.
Compatibility and Security Link to heading
SentinelOne fully complies with industry security standards and regulations. It works in compliance with regulations such as KVKK and GDPR and protects data by encrypting it. While the transmission of data is done with TLS 1.2/1.3, it is secured with AES-256 encryption in the cloud. Data retention period varies depending on the license package used.
SentinelOne also has certifications such as SOC 2 Type II, ISO 27001, FedRAMP High and supports compliance with security standards such as CMMC, HIPAA, PCI DSS.
